How to Identify Danger

Authored by Praesidium, this article underscores our shared dedication to equipping organizations with the tools and knowledge needed to prevent abuse.
What are the common characteristics of an offender?
If you stop and think about that question for a bit, you might realize you cannot tell an offender from anyone else just by looking at them. And guess what, most offenders don’t want to get caught. We'll talk about that in greater detail later, but privacy is the primary enabler to most offenders and “blending in” is a skill set that they master. The ones who don’t master this get caught.
You might be surprised to learn that:
- 60% of all sexually abused children are molested by someone that child already knows.
- Only 11% of sexually abused children are molested by a total stranger.
- Of the 60% of children molested by someone the child knows, 29% are molested by a family member.
These statics show us that the problem is embedded and increasingly difficult to identify. The focus shouldn't necessarily be on random strangers, but instead, on the relationships a child has formed within their circle of influence.
And it’s not just adults that we are concerned about anymore. According to Praesidium, Inc.™:
- 50% of sexual abuse is perpetrated by other youth.
- There is a 300% increase in the number of Peer-to-Peer abuse cases.
What we don’t know right now is if that 300% increase is due to the actual number of cases increasing, or if it's that more cases are being reported then were in the past. What we do know, however, is that the issue is significant and that our controls must now address these occurrences as well as adult-to-child occurrences.
What risk factors contribute to child sexual abuse?
There are three factors that contribute to the abuse of another person:
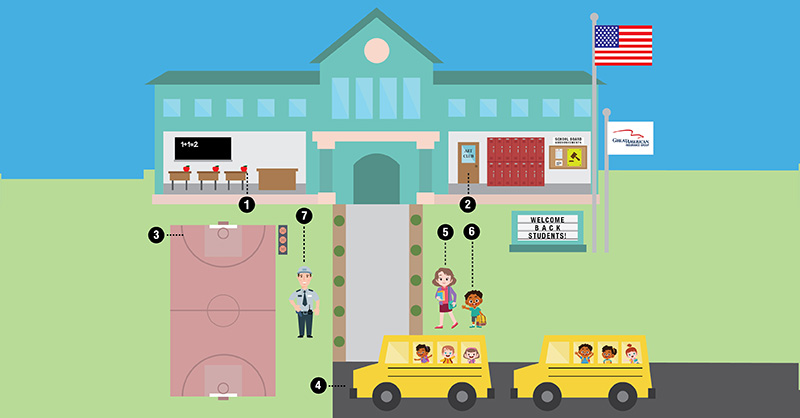
- Access – An offender needs to have access to the participant in order to interact with them.
- Control – An offender needs to be able to control the participant so that they can carry out abuse without the participant fleeing or telling others.
- Privacy – Offenders do not want to get caught. They need physical space that is isolated in order to conduct the abuse, and they need secrecy in order to continue abuse over time.
To help prevent abuse in your organization, take steps to interrupt Access, Control and Privacy among staff and volunteers.
Abuse Prevention: Plan. Protect. Respond.
Learn practical ways to help stop abuse in your community.